Key Risks in IT Outsourcing and How to Avoid Them
Businesses today increasingly look for cost-effective and scalable solutions to manage their IT needs. Outsourcing IT services is a proven strategy that provides access to specialized expertise, accelerates project timelines, and enhances operational agility. According to a report by Statista, the global IT outsourcing market is projected to reach approximately $806.55 billion by 2030, at a CAGR of about 6.51%.

However, outsourcing IT services is not without risks. Poor planning, miscommunication, and inadequate vendor management can lead to financial losses, security breaches, and missed business objectives. In this blog, we discuss the key risks in IT outsourcing and provide actionable steps on how to outsource IT services effectively while minimizing potential pitfalls.
1. Data Security and Privacy Risks
One of the most critical concerns when outsourcing IT is data security. Sharing sensitive business information, customer data, or intellectual property with a third-party provider exposes organizations to potential breaches, cyberattacks, or regulatory non-compliance.
How to mitigate this risk
- Vendor background checks: Verify the provider’s reputation, security certifications, and history with data protection.
- Data encryption: Use strong encryption protocols for data storage and transfer.
- Access control: Limit access to sensitive systems and establish role-based permissions.
- Legal contracts: Include data protection clauses in the service-level agreement (SLA) and specify liability in case of breaches.
By prioritizing data security, your company can reduce the likelihood of financial and reputational damage caused by unauthorized access or leaks.
2. Communication Barriers
Miscommunication is a common challenge in IT outsourcing, especially when the provider is in a different country or time zone. Misaligned expectations, language differences, or unclear project documentation can lead to delays and errors.
How to overcome this challenge
- Clear documentation: Maintain detailed requirements, workflows, and milestones.
- Regular meetings: Schedule video calls, weekly updates, and progress reports.
- Collaborative tools: Use project management platforms like Jira, Trello, or Asana for transparency.
- Single point of contact: Assign a dedicated liaison to handle communications and clarify doubts.
Good communication practices prevent misunderstandings and keep the project on track.
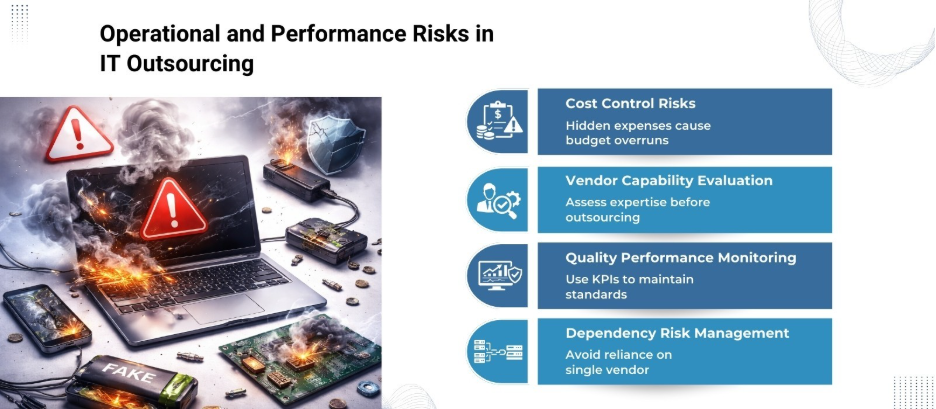
3. Hidden Costs and Budget Overruns
While IT outsourcing is often promoted as cost-effective, hidden costs can quickly accumulate. These may include vendor onboarding, software licensing, training, or additional work outside the initial scope. Without proper budgeting, outsourcing can become more expensive than anticipated.
How to control costs
- Detailed contracts: Specify deliverables, payment schedules, and penalties for scope changes.
- Transparent pricing models: Prefer fixed-price or milestone-based contracts over open-ended billing.
- Scope management: Clearly define project scope and manage change requests carefully.
- Regular financial tracking: Monitor invoices and project expenses consistently.
By tracking costs and documenting expectations upfront, your business can prevent budget surprises and maintain financial control over outsourced IT projects.
4. Quality and Performance Risks
Delivering high-quality IT solutions depends on technical expertise and adherence to best practices. Inadequate skills or substandard work can affect system performance, scalability, and user experience.
How to maintain quality
- Vendor evaluation: Assess technical expertise, certifications, and previous projects.
- Pilot projects: Start with smaller assignments to test the provider’s capabilities.
- Performance metrics: Define KPIs for response time, bug resolution, and project milestones.
- Regular audits: Conduct periodic reviews of code quality, testing results, and system performance.
Taking a structured approach to quality management helps maintain project standards and reduces the risk of errors or system failures.
5. Legal and Regulatory Compliance
Different countries have varied legal and regulatory requirements for data protection, labour laws, and intellectual property. Ignoring these regulations can lead to fines, litigation, or loss of business licenses.
How to manage compliance risks
- Legal consultation: Consult legal experts familiar with international IT regulations.
- SLA clauses: Include compliance obligations and liabilities in contracts.
- Data residency policies: Determine where data is stored and processed to comply with local laws.
- Regular audits: Ensure that outsourced operations follow regulatory standards consistently.
Compliance management safeguards your organization against legal challenges while supporting ethical business practices.
6. Dependency on External Providers
Outsourcing IT can create dependency on a third-party provider for critical operations. If the vendor underperforms, goes out of business, or abruptly terminates services, it may disrupt your operations.
How to reduce dependency
- Diversify vendors: Avoid relying solely on one provider for all critical services.
- Knowledge transfer: Maintain internal documentation and staff training.
- Exit strategy: Define a clear plan for transitioning services in case of vendor termination.
- Service continuity plans: Include disaster recovery and backup strategies in the contract.
A balanced approach to outsourcing allows your businesses to retain control over essential processes while leveraging external expertise.
7. Cultural and Time Zone Differences
When outsourcing to offshore vendors, cultural and time zone differences can affect collaboration and productivity. Misunderstandings, delays in responses, or conflicting work schedules may impact project delivery.
How to handle cultural and time differences
- Flexible scheduling: Plan overlapping working hours for meetings and updates.
- Cultural training: Educate teams about communication styles, work ethics, and business etiquette.
- Localized project managers: Employ managers who can bridge cultural gaps and facilitate smooth collaboration.
- Clear reporting structures: Define responsibilities and escalation procedures for efficient decision-making.
By addressing cultural and time zone challenges proactively, businesses can maintain workflow continuity and team harmony.
8. Intellectual Property Risks
Outsourcing IT can expose proprietary software, algorithms, and business ideas to third parties. Weak protection measures may lead to theft, misuse, or unauthorized distribution of intellectual property.
How to protect intellectual property
- Confidentiality agreements: Have vendors sign NDAs before starting work.
- IP ownership clauses: Clearly define ownership rights in the contract.
- Controlled access: Limit access to sensitive intellectual property to only necessary personnel.
- Regular monitoring: Track usage and modifications of proprietary materials during the project.
Proper IP management safeguards your company while facilitating collaboration with external providers.
How to Outsource IT Services Effectively
Knowing the risks is the first step. Implementing structured processes on how to outsource IT services allows businesses to capitalize on its benefits while minimizing exposure to potential pitfalls. Here are actionable steps:
- Define Objectives Clearly: Identify which IT functions or projects to outsource and what outcomes you expect.
- Vendor Selection: Evaluate technical expertise, financial stability, client feedback, and compliance with industry standards.
- Contract Negotiation: Include clear service-level agreements, pricing structures, and legal obligations.
- Communication Strategy: Set regular reporting schedules, collaboration tools, and escalation protocols.
- Quality Control: Implement performance monitoring, audits, and KPIs for timely feedback and adjustments.
- Security Measures: Encrypt data, restrict access, and conduct security audits periodically.
- Continuous Improvement: Encourage collaboration with the provider to adapt to evolving business needs and technology trends.
| Step | Action | Key Benefits |
| 1 | Define Objectives Clearly – Identify IT functions or projects to outsource and expected outcomes | Aligns outsourcing with business goals, avoids unnecessary services |
| 2 | Vendor Selection – Evaluate technical expertise, financial stability, client feedback, and compliance | Reduces risks, ensures skilled and reliable partners |
| 3 | Contract Negotiation – Include SLAs, pricing, and legal obligations | Prevents misunderstandings, protects your business legally |
| 4 | Communication Strategy – Set reporting schedules, collaboration tools, and escalation protocols | Improves transparency and project tracking |
| 5 | Quality Control – Implement KPIs, audits, and performance monitoring | Maintains high standards and system reliability |
| 6 | Security Measures – Encrypt data, restrict access, conduct security audits | Protects sensitive data and reduces cyber risk |
| 7 | Continuous Improvement – Collaborate with provider to adapt to evolving business needs | Keeps IT operations aligned with business growth |
A well-structured outsourcing strategy allows businesses to leverage specialized IT skills, reduce operational costs, and accelerate project delivery without compromising security or quality.

Take the Next Step with Nurture IT
Managing IT outsourcing risks doesn’t have to be overwhelming. With Nurture IT in Indiranagar, you get a trusted partner who provides end-to-end IT solutions, robust security measures, and expert support tailored to your business needs. Connect with us today to outsource your IT services confidently, reduce risks, and accelerate your digital transformation.
FAQs
1: What are the biggest risks in IT outsourcing?
The main risks include data security breaches, miscommunication, hidden costs, quality issues, compliance violations, vendor dependency, and IP exposure.
2: How can I minimize data security risks when outsourcing IT?
Use encrypted data transfer, restrict access, verify vendor security certifications, and include data protection clauses in your contracts.
3: What should I consider when selecting an IT outsourcing provider?
Assess technical expertise, previous projects, client feedback, financial stability, and compliance with industry standards.
4: How do hidden costs affect IT outsourcing?
Unexpected expenses like onboarding, software licensing, or extra work outside the contract can increase the overall cost significantly.
5: How can businesses maintain quality while outsourcing IT?
Set KPIs, start with pilot projects, conduct regular audits, and track performance metrics throughout the project.